1. Introduction
Two-Factor Authentication (2FA) enhances account security in Znode by requiring users to verify their identity through two authentication steps before accessing the system.
Instead of relying solely on passwords, 2FA introduces an additional verification layer that confirms the legitimacy of the login attempt.
- Username and password
- A one-time verification code sent to the registered email address
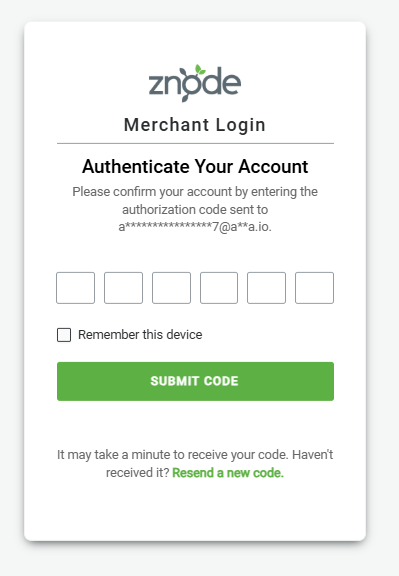
Once credentials are validated, the system sends a verification code to the user's email address. Access is granted only after the correct code is entered.
Why Two-Factor Authentication Matters
- Protection against compromised credentials
- Defense against brute-force password attacks
- Prevention of credential reuse across websites
- Reduced risk from phishing attacks
- Protection from automated bot login attempts
Currently, Znode supports email-based verification codes. SMS-based authentication is planned for future releases.
2. Key Capabilities
- Email-based verification codes
- Configurable verification code expiration
- Configurable resend code cooldown period
- Limit on failed authentication attempts
- Temporary account lockout after multiple failures
- Trusted device functionality (“Remember My Device”)
- Separate configuration for Admin Console and Storefront
- Automatic email notifications
- Support across Admin Console, Storefront, B Store, and Commerce Portal
3. Configuration Locations
All Two-Factor Authentication settings are managed through the Admin Console.
| Configuration Area | Applies To |
|---|---|
| Global Settings | Admin Console Users |
| Store Settings | Storefront, B Store Shoppers |
Settings appear under the section titled Two Factor Authentication Settings.
4. Admin Console Configuration
4.1 Enable Two-Factor Authentication
Default Value: NO
When Enabled
- Admin enters username and password
- System validates credentials
- A 6-digit verification code is generated
- The code is emailed to the registered email address
- The admin must enter the code to complete login
When Disabled
Login requires only a username and password.
4.2 Verification Code Timeout
Default: 10 minutes
Range: 1 – 360 minutes
"Your authentication code timed out. Kindly generate a new code to continue."
4.3 Trusted Device Validity Period
Default: 2 days
Range: 1 – 365 days
This defines how long a device remains trusted when the user selects Remember My Device.
4.4 Limit on Failed Attempts
Default: 3 attempts
If this limit is exceeded, the account is temporarily locked.
4.5 Temporary Lockout Period
Default: 30 minutes
Users cannot attempt login until the lockout period expires.
4.6 Resend Code Cooldown
Default: 30 seconds
Prevents users from repeatedly requesting verification codes.
5. Admin Console Login Workflow
- Admin enters username and password
- Credentials are validated
- System generates a 6-digit verification code
- Code is sent to the registered email
- Admin enters the code on the verification screen
Possible Outcomes
- Successful Login: Redirected to Admin Dashboard
- Incorrect Code: “Invalid authentication code, X attempts left to login.”
- Expired Code: User must request a new code
- Too Many Failed Attempts: Account temporarily locked
6. Resend Verification Code Behavior
- The Resend Code option appears only after an attempt to enter a code.
- A cooldown timer prevents repeated requests.
- When a new code is issued, all previous codes become invalid.
7. Remember My Device
When the user selects Remember My Device during authentication:
- The device is marked as trusted
- 2FA will not be required for the configured validity period
- After the period expires, verification will be required again
8. Forgot Password Workflow
- User resets password
- System displays “Password reset successfully”
- User is redirected to login
- 2FA verification is required during next login
9. Future Enhancements
- SMS-based verification codes
- Text message OTP authentication
- Administrative account unlock override
- Support for additional authentication methods
